The Nerd Who Built a Drug Empire From His Laptop


And how a Gmail address brought the whole thing down.
Imagine this: a 27-year-old physics graduate, sitting alone in his apartment, convinced he could build something that would change the world. Not an app. Not a startup. A black market — fully anonymous, completely untraceable, and philosophically justified. He called it Silk Road.
And for about two and a half years, it worked.
A Libertarian With a God Complex
Ross Ulbricht wasn't your typical criminal. He wasn't a cartel boss. He didn't come up through the streets. He was a soft-spoken guy from Austin, Texas, who read too much Ludwig von Mises and got deeply convinced that governments had no right to tell you what to put in your own body.
His philosophy had a name: agorism — the idea that the real path to political freedom isn't through elections or protests, but through building underground markets that operate completely outside state control. To Ross, Silk Road wasn't a drug website. It was a political statement.
He even kept a personal journal where he described his goal as building an "economic simulation" — a place where people could trade freely, without the threat of government coercion. He adopted the alias Dread Pirate Roberts, borrowed from The Princess Bride — a character whose identity gets passed down so the legend lives forever, untied to any single person.
Grand vision. Terrible OPSEC.
The Tech Stack That Should Have Been Untouchable
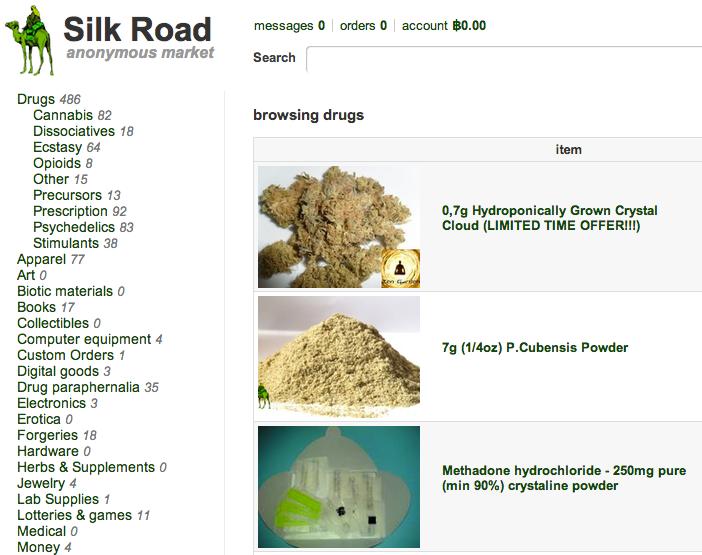
Here's where it gets genuinely impressive from a technical standpoint. Silk Road launched in early 2011 built on two technologies that, at the time, were barely on anyone's radar: Tor and Bitcoin.
Tor — The Onion Router — works by bouncing your traffic through multiple encrypted layers across international relay nodes. Each node only knows the one before it and the one after it. Nobody sees the full path. The server's physical location stays invisible. In theory, you simply cannot trace it with standard DNS lookups or IP scanning.

Bitcoin handled the money. As a decentralized currency with no KYC requirements, it let buyers and sellers move value without touching a bank. Yes, the blockchain is public — every transaction is recorded forever — but wallet addresses are pseudonymous. Nobody knows who owns what, as long as you never link your wallet to your real identity.
To make it even harder to trace, Silk Road built an internal Bitcoin tumbler. It would break your payment into tiny fragments, mix them with other users' funds, and reassemble them at the destination. Forensic blockchain analysis became a nightmare.
The trust layer was clever too. No legal contracts exist in an anonymous black market, so Silk Road used economics instead:
- An escrow system held buyer funds until delivery was confirmed
- A reputation system let community reviews punish scammers and reward reliable sellers

At its peak in September 2013, Silk Road had nearly 13,000 drug listings, over 957,000 registered users, and had processed roughly $1.2 billion in total transactions. Ulbricht himself pocketed around $80 million in commissions — all in Bitcoin.
The FBI called it the "Amazon of narcotics." They weren't wrong.
The Email That Ended Everything
For all its technical sophistication, Silk Road was sunk by something embarrassingly basic.
IRS agent Gary Alford started digging into the very early days of Silk Road's promotion. He found a username called "Altoid" on Bitcointalk forums, posting about this cool new anonymous drug marketplace back in January 2011. Normal enough. Then, a few months later, the same "Altoid" account posted a job listing on the same forum — and attached a contact email: rossulbricht@gmail.com.
That was it. That was the thread that unraveled everything.
From there, investigators found his LinkedIn profile, where he openly discussed using economic theory to "eliminate coercive institutions." They compared it to the libertarian manifestos DPR had posted on Silk Road's forums. The writing style, the philosophy, the timing — it all lined up.
The lesson here isn't complicated: your real-world identity and your anonymous online identity cannot ever touch. One slip — one email address, one forum post, one reused username — and the whole architecture of anonymity collapses. Doesn't matter how bulletproof your Tor setup is.
The Arrest: A Masterclass in Social Engineering
By October 1, 2013, federal agents knew who Ross Ulbricht was. The challenge wasn't finding him — it was catching him with his laptop open.
If he closed the lid, full-disk encryption would lock everything. Every piece of evidence gone. So investigators tracked him to the Glen Park Public Library in San Francisco, where he regularly managed Silk Road over public Wi-Fi. They watched his screen. They waited until he was logged in as "Mastermind" — the administrative account.

Then, two undercover agents staged a loud, physical fight directly behind him. Ulbricht spun around. In that moment, a third agent grabbed the open laptop and handed it directly to a forensics tech.
Inside: admin panel access, a daily activity log going back to 2011, financial spreadsheets, Bitcoin private keys holding over 144,000 BTC, and chat logs discussing fake IDs and — more disturbingly — instructions related to murder-for-hire.
The jury deliberated for less than four hours. On May 29, 2015, Ulbricht was sentenced to life in prison without parole.
The Cops Who Went Rogue
Here's a plot twist that almost feels scripted: two of the federal agents investigating Silk Road were quietly stealing from it.
Carl Mark Force IV (DEA) created unauthorized personas — including one called "French Maid" — to build rapport with DPR. He then sold Ulbricht supposed inside information about the investigation for $100,000 in Bitcoin, and tried to extort another $250,000 under threat of leaking information.
Shaun Bridges (Secret Service), a computer forensics expert, gained access to Silk Road admin accounts after another arrest. Instead of securing the assets for evidence, he quietly drained thousands of Bitcoin into his personal accounts via Mt. Gox. His take: over $820,000.
Both were eventually convicted. But their actions gave Ulbricht's defense team a legitimate argument that the investigation had been compromised from the inside — a claim that, while ultimately unsuccessful, raised serious questions about the integrity of the whole case.
The Pandora's Box Problem
Silk Road shut down in October 2013. Within weeks, Silk Road 2.0 was already online, run by former administrators of the original. When that one fell a year later, dozens more took its place.
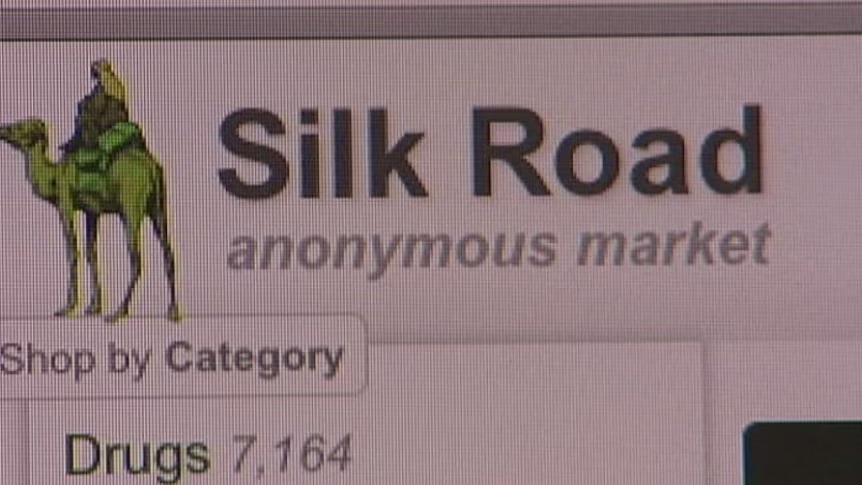
The successors learned from Ulbricht's mistakes. They adopted Monero — a privacy coin that obscures sender, receiver, and transaction amount at the protocol level, making Bitcoin's pseudonymity look quaint by comparison. They implemented multi-signature escrow to prevent operators from pulling exit scams. Some even experimented with fully decentralized architectures with no single server to seize.
AlphaBay eventually surpassed Silk Road's transaction volume. Hydra ran for eight years out of Russia before German authorities took it down in 2022. The template Ulbricht built became the blueprint for an entire industry.
What It Actually Means
In January 2025, Donald Trump granted Ross Ulbricht a full pardon. After 11 years in prison, he walked free. For libertarian and digital rights communities, it was a symbolic victory. For everyone else, the debate over whether life without parole fit the crime continues.
But here's the bigger picture: Silk Road wasn't just a drug market. It was a proof of concept — a live demonstration that cryptographic tools could let people build entire economic systems beyond the reach of governments. The ideological DNA of Silk Road lives on in every decentralized protocol, every privacy-focused tool, every debate about self-sovereignty and state power in the digital age.
From a cybersecurity perspective, the story is a perfect case study in how operational security is only as strong as its weakest human link. Tor is solid. Bitcoin is clever. But one careless email address, one compromised agent, one staged library argument — and the whole fortress falls.
The internet didn't get safer after Silk Road closed. It got more sophisticated.
And that's the part worth paying attention to.
Sources: Wikipedia, FBI forensic case files, DOJ press releases, Krebs on Security, Harvard JOLT.